Cracking the Code to Cybersecurity: Mastering the Art of Threat Detection and Response
Cracking the Code to Cybersecurity: Mastering the Art of Threat Detection and Response
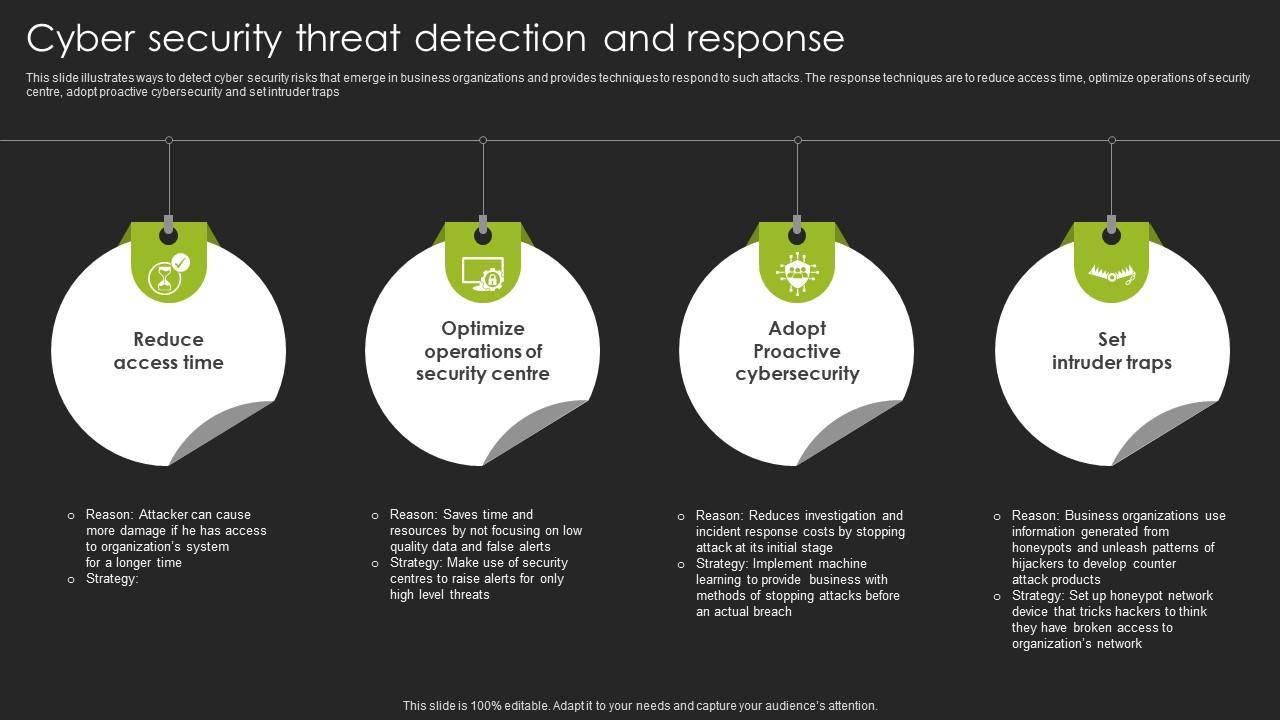
In today's digital age, cybersecurity threats are becoming increasingly sophisticated and frequent, posing a significant risk to businesses, organizations, and individuals. As technology advances, so do the tactics used by cyber attackers, making it essential for organizations to stay one step ahead in detecting and responding to threats. According to a report by Cybersecurity Ventures, the global cybercrime damage is expected to cost $10.5 trillion by 2025, a staggering increase from the 2015 estimate of $3 trillion. As this figure continues to rise, organizations must prioritize investing in robust cybersecurity measures to protect their assets.
Cybersecurity is not just a challenge, but an opportunity for organizations to demonstrate their commitment to protecting their customers' data and maintaining a reputation of trust. By implementing effective threat detection and response strategies, organizations can not only protect themselves from cyber threats but also gain a competitive edge in their respective industries. In an interview with a cybersecurity expert, John Hammond, a Senior Security Researcher at Kngine, highlighted the importance of threat detection and response, stating, "Threat detection and response is not just a technical exercise, but an art that requires a deep understanding of an attacker's motivations and tactics."
To crack the code of cybersecurity, organizations must adopt a multi-layered approach to threat detection and response. This involves investing in cutting-edge technology, training a skilled workforce, and fostering a culture of cybersecurity awareness throughout the organization.
Protecting Assets with Advanced Technology
To effectively detect and respond to threats, organizations must invest in advanced technology that provides real-time monitoring and detection capabilities. Some key technologies to consider include:
* **Machine Learning and Artificial Intelligence (AI)**: These technologies enable organizations to analyze vast amounts of data, identify patterns, and detect anomalies that may indicate a potential threat.
* **Security Orchestration, Automation, and Response (SOAR)**: SOAR platforms help streamline security operations by automating repetitive tasks, improving incident response times, and enhancing collaboration between teams.
* **Cloud Security**: Organizations must ensure that their cloud infrastructures are secure by using cloud security solutions that provide visibility, detection, and response capabilities.
* **Endpoint Detection and Response (EDR)**: EDR solutions provide real-time monitoring and detection of endpoint threats, enabling organizations to respond quickly to potential threats.
* **Network Traffic Analysis**: This involves monitoring network traffic to detect potential threats and identify areas where attacks may be originating.
"In today's threat landscape, organizations must invest in advanced technologies that provide real-time monitoring and detection capabilities," said Mikko Hyppönen, a renowned cybersecurity expert. "By doing so, they can stay ahead of the evolving threats and protect their assets effectively."
Training a Skilled Workforce: A Critical Component
Having a skilled workforce is essential for effective threat detection and response. Organizations must invest in employee training and development programs that provide cybersecurity awareness, threat detection, and incident response skills. Some key training areas to focus on include:
* **Cybersecurity Fundamentals**: Employees must understand basic cybersecurity concepts, protocols, and best practices to effectively respond to potential threats.
* **Threat Detection and Incident Response**: Employees must be trained to detect potential threats and respond effectively in the event of a breach.
* **Communication and Collaboration**: Employees must learn to communicate effectively with stakeholders and collaborate with various teams to ensure smooth incident response processes.
"A skilled workforce is critical to effective threat detection and response," said Dr. Gary Ellison, a renowned cybersecurity expert. "Employee training and development programs are essential for enabling employees to stay ahead of the evolving threats and protect organizational assets."
Building a Culture of Cybersecurity Awareness
Fostering a culture of cybersecurity awareness is critical for effective threat detection and response. Organizations must promote a culture of cybersecurity awareness throughout the organization by:
* **Conducting Regular Security Awareness Training**: Provide regular training sessions to educate employees on basic cybersecurity concepts, best practices, and potential threats.
* **Promoting Cybersecurity Best Practices**: Encourage employees to follow cybersecurity best practices, such as using strong passwords, avoiding phishing emails, and being cautious when clicking on links.
* **Establishing Security Incident Response Teams**: Establish clear incident response procedures and establish security incident response teams to respond quickly to potential threats.
"Cybersecurity awareness is not just a technical issue, but an organizational culture that requires everyone's participation to protect organizational assets," said José Lorusso, a cybersecurity expert.
Conclusion
Cracking the code to cybersecurity requires organizations to adopt a multi-layered approach to threat detection and response. By investing in advanced technology, training a skilled workforce, and fostering a culture of cybersecurity awareness, organizations can effectively detect and respond to threats, protecting their assets and maintaining a reputation of trust. As the threat landscape continues to evolve, organizations must prioritize investing in robust cybersecurity measures to stay ahead of the attacks and protect their digital identities.


Related Post

Customer Service 3.0: The Csms Revolutionizing The Way We Interact With Brands

Czech Porn Street: Unveiling the Dark Side of the Czech Republic's Porn Industry

Unveiling Season Hubley Today: The Iconic Actress Of The 70s And 80s

Cathie Wood's Rise to Wealth: A Look at Her Net Worth and Investment Strategies

